What Happens Inside a Professional Data Sanitization Facility?
Most people imagine data destruction as a simple process: plug in a drive, click “Erase,” and throw the disk away.
Reality is very different.
Inside a professional data sanitization facility, hundreds — sometimes thousands — of drives move through carefully designed workflows involving intake verification, inventory tracking, parallel erasure systems, compliance validation, and automated reporting.
This is not just deleting files.
It is industrial-scale data security.
Step 1 — Intake and Inventory
The process begins long before any erase command is issued.
Drives arriving at a sanitization facility are typically:
- removed from corporate PCs*
- decommissioned from servers
- retired from data centers
- collected from government agencies
- processed by ITAD and recycling companies
Each device must first be identified and logged.
Typical intake workflow includes:
- barcode scanning
- serial number capture
- drive type identification
- capacity verification
- customer association
- chain-of-custody tracking
In professional environments, losing track of even a single drive may create compliance risks.
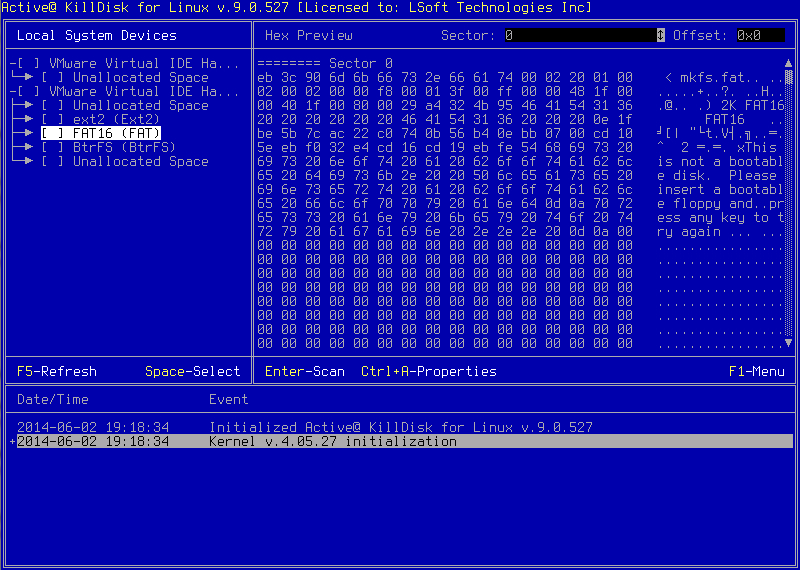
Step 2 — Sorting by Media Type

Modern facilities rarely process all drives the same way.
Different storage technologies require different sanitization methods.
Typical categories include:
- SATA HDDs
- SAS enterprise drives
- SATA SSDs
- NVMe SSDs
- USB external drives
- failed or partially damaged devices
This matters because sanitization behavior differs significantly between HDDs and SSDs.
For example:
- traditional overwrite methods work well for HDDs
- SSDs often require firmware-level sanitize commands
- damaged drives may require physical destruction
Efficient facilities optimize workflows based on media type.
Step 3 — Connecting Hundreds of Drives
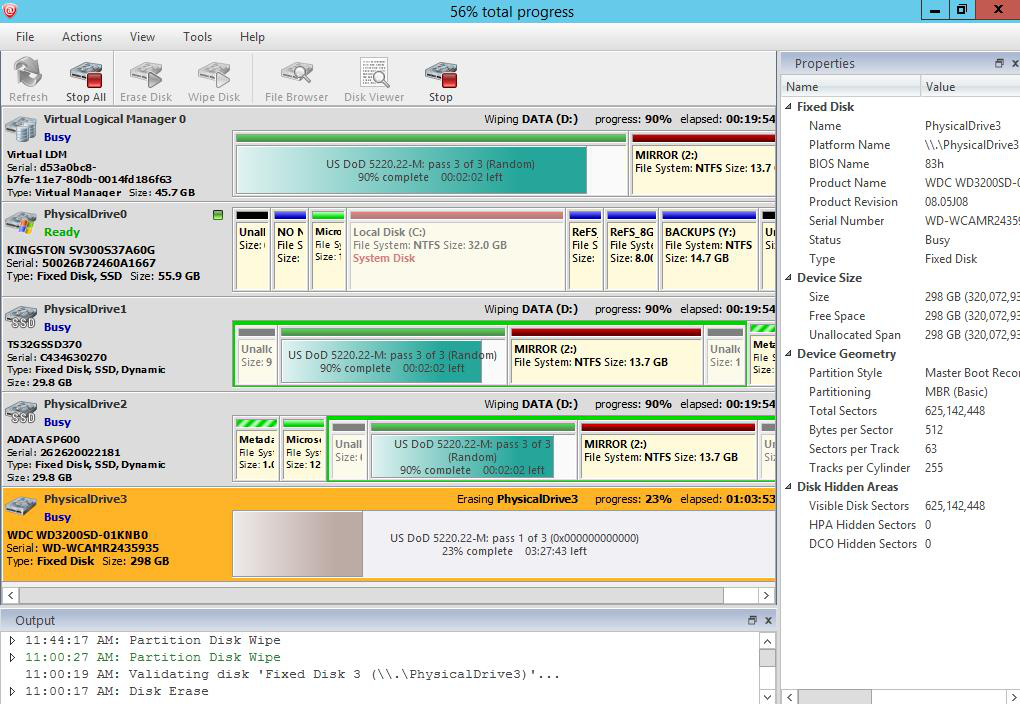
This is where industrial-scale sanitization becomes impressive.
Professional facilities use:
- high-density erase stations
- disk arrays
- hot-swap bays
- parallel sanitization systems
- rack-mounted hardware
Some operations process dozens or even hundreds of drives simultaneously.
Instead of manually erasing one disk at a time, operators use centralized systems capable of:
- monitoring all devices
- launching batch erase jobs
- tracking progress in real time
- generating automated reports
Speed and scalability become critical.
Step 4 — Health Checks and Verification
Before sanitization begins, drives are often tested for:
- SMART health status
- bad sectors
- communication errors
- firmware accessibility
- interface stability
Why?
Because failed or unstable drives may not sanitize reliably.
Professional workflows must identify:
- drives that can be securely erased
- drives that require additional verification
- drives that must be physically destroyed
This stage helps prevent false assumptions about successful sanitization.
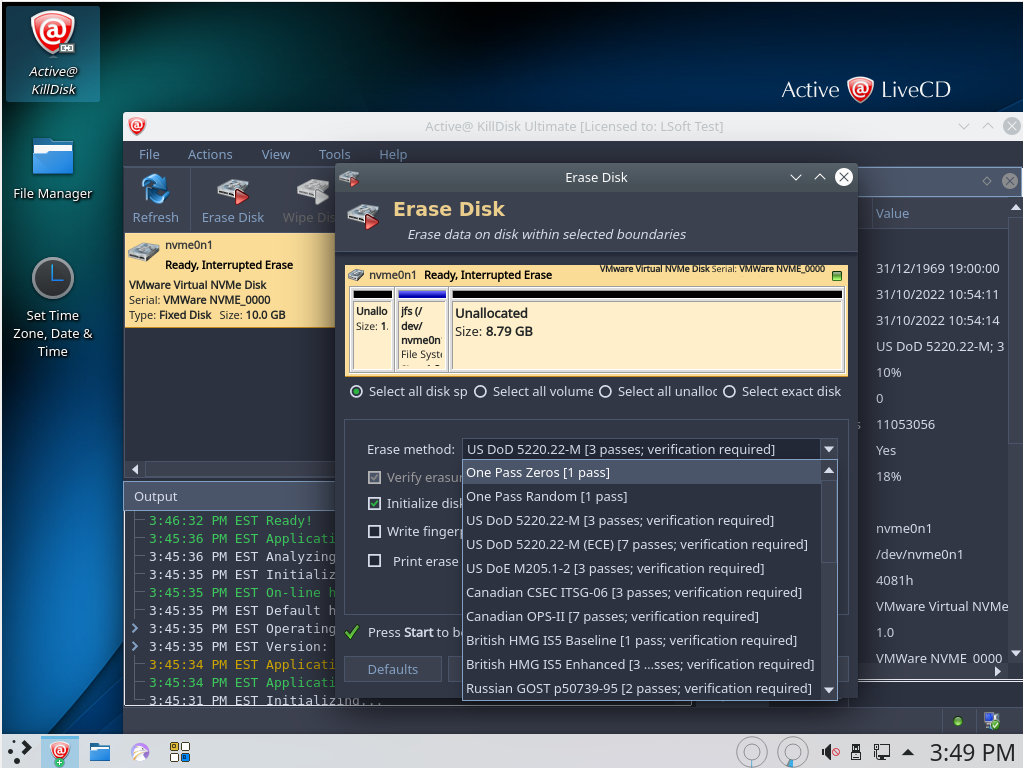
Step 5 — The Actual Sanitization Process
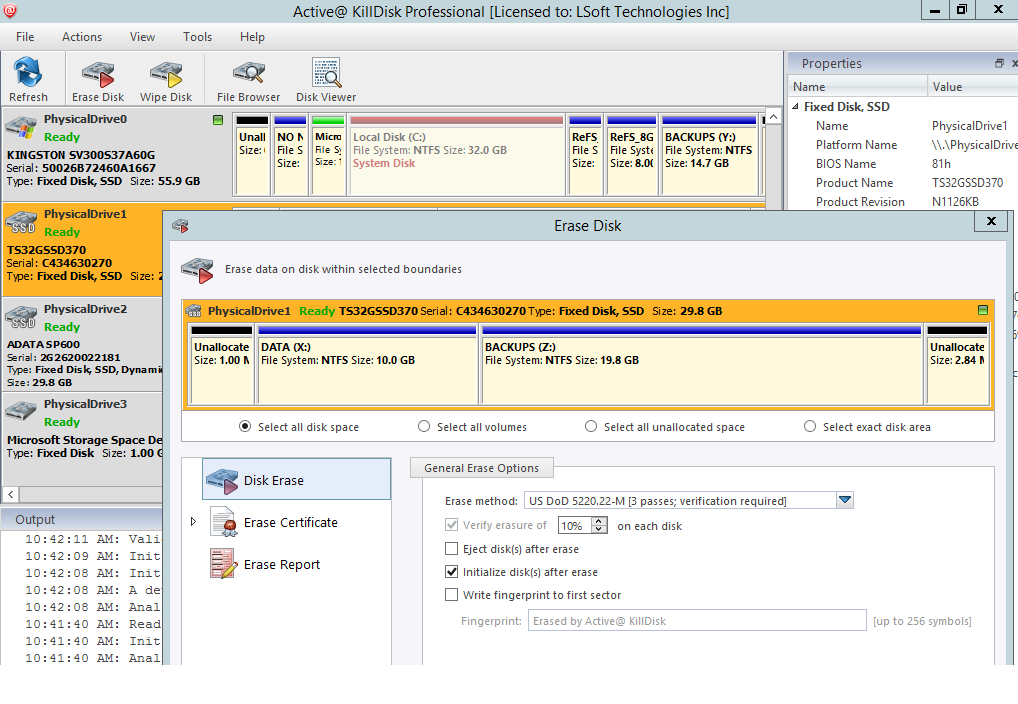
Now the real work begins.
Depending on policy requirements and drive type, facilities may use:
- One-pass overwrite
- NIST-aligned erase procedures
- ATA Secure Erase
- NVMe Sanitize
- Cryptographic Erase
- Custom overwrite patterns
Modern workflows increasingly favor:
- firmware-based sanitization
- media-aware methods
- verification-driven workflows
Contrary to popular belief, endless overwrite passes are usually unnecessary for modern storage devices.
The objective is not simply “more passes.”
The objective is secure, verifiable, scalable sanitization.
Step 6 — Verification and Audit Logging
This is one of the most important parts of professional sanitization.
Anyone can claim a drive was erased.
Professional facilities must prove it.
After sanitization, systems perform verification procedures and generate:
- erase reports
- audit logs
- certificates of sanitization
- serial-number tracking
- operation timestamps
- operator identification
This documentation becomes essential for:
- compliance audits
- enterprise contracts
- government requirements
- legal protection
- chain-of-custody validation
In many environments, reporting matters just as much as the erase operation itself.
Step 7 — Failed Drives and Physical Destruction
Not every drive can be sanitized successfully.
Some devices may:
- fail initialization
- contain unreadable sectors
- experience controller damage
- refuse sanitize commands
In these cases, facilities often escalate to:
- shredding
- crushing
- degaussing
- physical destruction workflows
Modern sanitization operations typically combine software erasure and physical destruction procedures.
Step 8 — Final Disposition
Once sanitization is complete, devices typically follow one of several paths:
- hardware recycling
- resale
- corporate redeployment
- certified disposal
- component harvesting
At this stage, sanitization certificates and audit reports become part of the permanent operational record.
For large organizations, this documentation may be retained for years.
Why Industrial Sanitization Matters
Modern organizations handle enormous volumes of sensitive data.
A single improperly erased drive may expose:
- customer databases
- financial records
- internal communications
- healthcare information
- intellectual property
- government data
Professional sanitization facilities exist to reduce that risk through:
- standardized workflows
- automation
- verification
- reporting
- scalability
This is why enterprise-grade solutions like Active@ KillDisk are designed not just to erase data — but to support the entire sanitization lifecycle.
Conclusion
Professional data sanitization is far more sophisticated than most people realize.
Behind every successfully erased drive is a workflow involving:
- inventory control
- hardware management
- erase automation
- verification systems
- compliance reporting
- operational scalability
As storage volumes continue to grow, industrial sanitization facilities will play an increasingly critical role in enterprise cybersecurity and data lifecycle management.
